Introduction
In an age of advancing technology, waste management has evolved beyond simple bin collections. Newest Custom RFID Waste Bin Tags have emerged as a transformative solution, revolutionizing the industry. While their ability to optimize waste collection and reduce costs is widely recognized, it’s equally essential to understand how these tags address data security and privacy concerns in waste management processes. In this comprehensive exploration, we delve into the innovative ways Bespoke RFID Waste Bin Tags safeguard sensitive information, ensuring a secure and efficient waste management ecosystem.

I. The Power of Custom RFID Waste Bin Tags
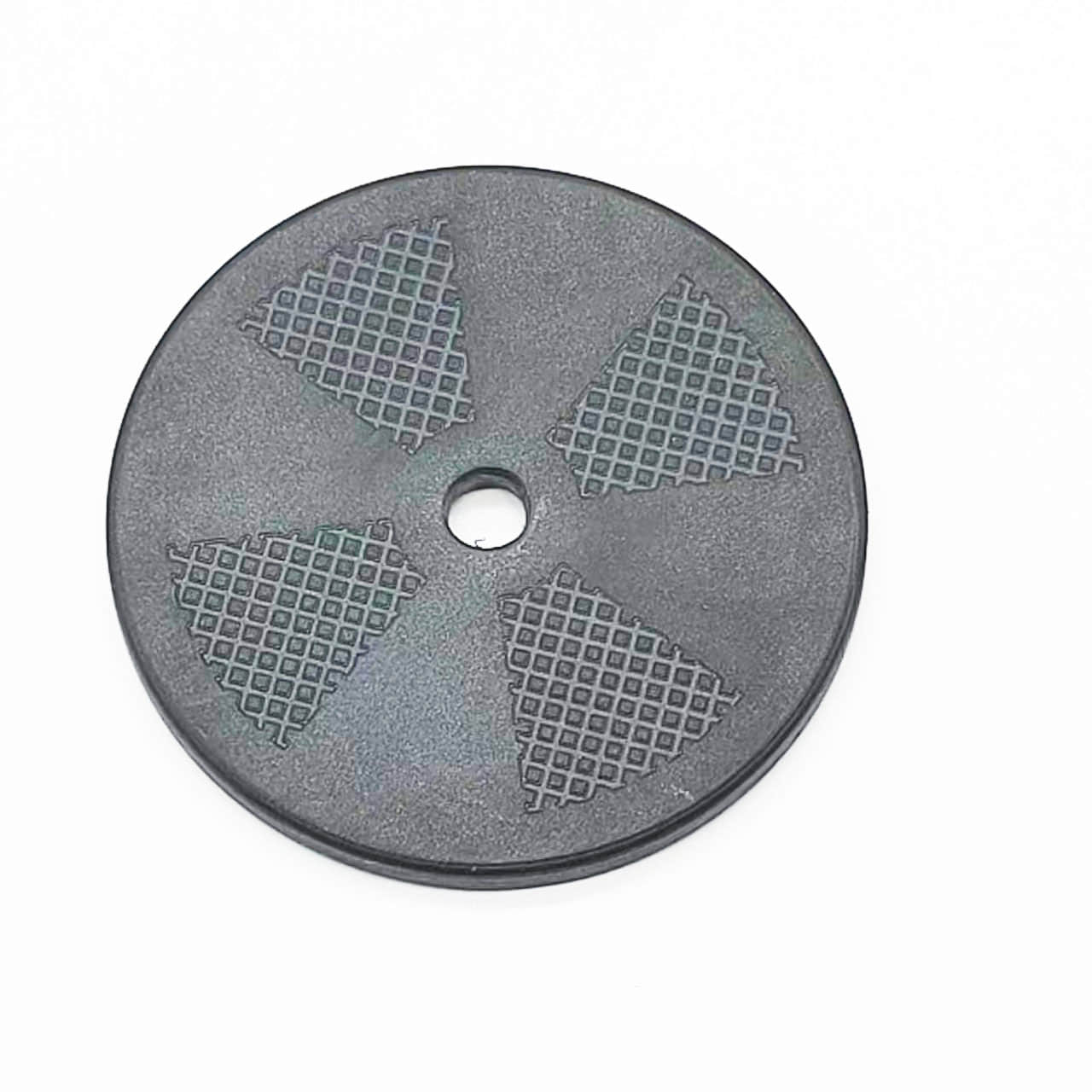
Custom RFID Waste Bin Tags represent a pioneering approach to waste management. By incorporating RFID technology, these tags enable real-time tracking, monitoring, and management of waste collection processes. They are designed for customization to meet specific requirements, making them adaptable to diverse waste management scenarios. Before diving into their data security features, let’s briefly revisit their key attributes.
- Customization:
These tags can be tailored to the unique needs of businesses, municipalities, and industries. Customization ensures they seamlessly integrate with different types and sizes of waste bins, maintaining both functionality and aesthetics.
- RFID Technology:
Bespoke RFID Waste Bin Tags leverage RFID technology, allowing for efficient data capture and communication. This technology plays a pivotal role in optimizing waste management processes.
- Durability:
Engineered to withstand harsh environmental conditions, these tags have a long service life, reducing the need for frequent replacements.
- Data Security:
These tags employ advanced security measures to protect sensitive data from unauthorized access and tampering, ensuring privacy and compliance with regulations.
II. Data Security Measures
To comprehend how Custom RFID Waste Bin Tags address data security and privacy concerns, it’s vital to explore the specific measures and mechanisms they employ:
- Authentication and Authorization:
Bespoke RFID Waste Bin Tags use authentication protocols to ensure that only authorized personnel can access sensitive data. This includes using encrypted authentication keys and access controls to prevent unauthorized access.
- Encryption:
Data transmitted by these tags is encrypted, rendering it unreadable to anyone attempting to intercept it. This encryption secures data during transmission between the tags, readers, and centralized databases.
- Secure Data Storage:
Collected data is stored in centralized databases with robust security measures in place. These databases are protected against external threats, ensuring data integrity and confidentiality.
- Audit Trails:
Bespoke RFID Waste Bin Tags maintain comprehensive audit trails that record all interactions with the data. This feature not only aids in monitoring but also assists in identifying any unauthorized access or potential breaches.
III. Privacy Concerns and Compliance
In addition to data security, Bespoke RFID Waste Bin Tags address privacy concerns associated with waste management data:
- Data Minimization:
These tags collect only essential data, minimizing the amount of sensitive information stored. This aligns with privacy principles by reducing the risk of collecting excessive or unnecessary data.
- Data Retention Policies:
Custom RFID Waste Bin Tags adhere to stringent data retention policies, ensuring that data is retained only for as long as necessary. This prevents the accumulation of outdated or irrelevant information.
- User Consent:
In scenarios where waste management involves personal data, such as in residential collections, user consent mechanisms can be integrated, ensuring compliance with privacy regulations.
IV. Compliance with Regulations
Custom RFID Waste Bin Tags are designed to align with data protection regulations, including GDPR, HIPAA, and local privacy laws. Their data security and privacy features are essential for organizations and municipalities seeking to meet legal requirements while enhancing waste management efficiency.
V. Transparency and Education
To foster trust and transparency, organizations and municipalities deploying Custom RFID Waste Bin Tags often engage in educational initiatives. These programs aim to inform residents and stakeholders about data collection processes, privacy safeguards, and how their data is being used. Educating the public about the benefits and safeguards in place can alleviate concerns and build confidence in the technology.

VI. Addressing Public Concerns
While the data security and privacy measures in Custom RFID Waste Bin Tags are robust, public perception and concerns are important factors to consider. To maintain public trust, it is crucial for organizations and municipalities to engage in open dialogues with residents and stakeholders. Here are some strategies to address public concerns:
- Transparency:
Clearly communicate the purpose and benefits of Bespoke RFID Waste Bin Tags to the public. Explain how data is collected, used, and protected. Offer channels for residents to seek clarification and express their concerns.
- Data Access and Control:
Provide residents with the option to access their own data and control how it is used. Offering tools for individuals to manage their data builds trust and empowers them.
- Privacy Impact Assessments:
Conduct privacy impact assessments to identify and mitigate potential privacy risks. Share the results with the public to demonstrate commitment to data protection.
- Anonymization:
Whenever possible, employ anonymization techniques to dissociate data from individual identities, further enhancing privacy protection.
- Regular Audits:
Conduct periodic privacy and security audits to ensure ongoing compliance with data protection regulations. Share the results of these audits with the public to demonstrate accountability.
VII. The Path Forward
As we continue to navigate the complex landscape of waste management and data privacy, Custom RFID Waste Bin Tags serve as a model for responsible technology adoption. They showcase how it is possible to harness the power of data for operational efficiency while respecting individuals’ privacy rights. The coexistence of efficient waste management and robust data security and privacy measures is not just possible; it is essential for the future.
VIII. Conclusion
Custom RFID Waste Bin Tags are not just about optimizing waste management; they are also about protecting sensitive data and respecting individual privacy rights. Their sophisticated data security measures, compliance with regulations, and commitment to transparency make them a reliable and responsible solution for the challenges of modern waste management.
In summary, Custom RFID Waste Bin Tags offer a groundbreaking solution that goes beyond streamlining waste management; they prioritize data security, privacy, and compliance with regulations. Their advanced security measures, commitment to transparency, and ability to strike a balance between efficiency and privacy make them a responsible and reliable choice for modern waste management challenges. These tags not only enhance operational efficiency but also ensure the protection of sensitive information, contributing to a cleaner, more sustainable future in waste management. Embracing technology that upholds both operational excellence and individual privacy rights is key to advancing responsibly in our data-driven world, and Bespoke RFID Waste Bin Tags exemplify this commitment.